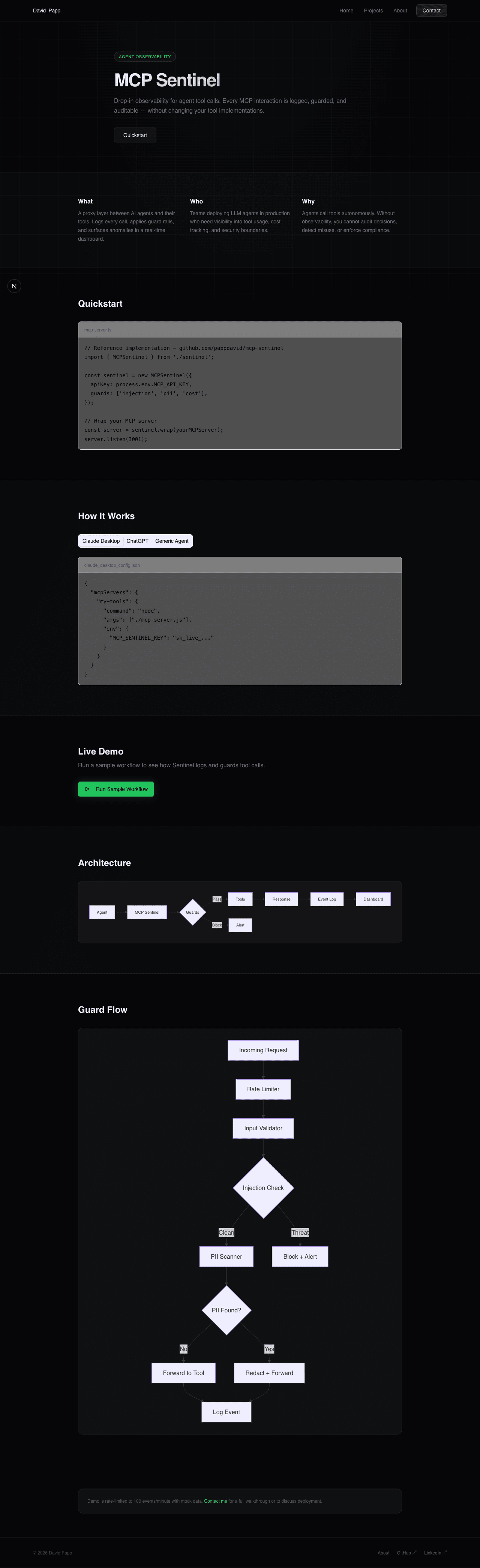
MCP Sentinel
A proxy layer for Model Context Protocol that logs, guards, and audits every agent tool call in real time.
My role: Solo project — designed and built to explore agent observability patterns.
Problem
AI agents running in production make hundreds of tool calls per hour. Without visibility, injection attacks, runaway costs, and PII leaks go undetected until they cause real damage. Existing logging solutions don't understand the MCP protocol structure.
What this demonstrates
- Designing a composable middleware pipeline that is extensible without modifying existing guards
- Integrating Upstash Redis sliding-window rate limiting in a Next.js edge-compatible context
- Supabase RLS as a security boundary — dashboard only shows events for the authenticated API key owner
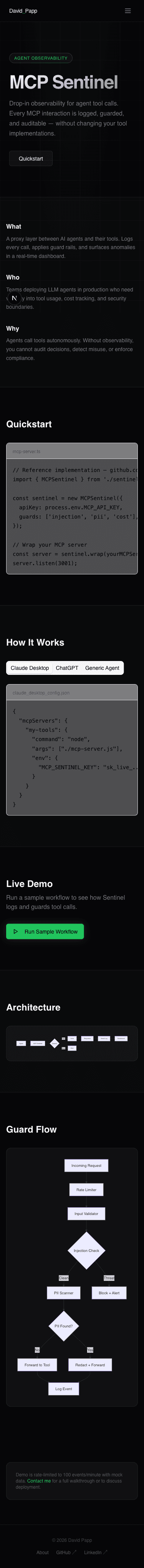
Architecture
Tech stack rationale
- TypeScript + Next.js: API routes act as the proxy layer; type safety enforced across the full guard pipeline.
- Supabase: Event storage with row-level security; each API key can only query its own events.
- Upstash Redis: Serverless-compatible sliding-window rate limiter; no persistent connection required.
- Clerk: Auth; the dashboard is protected and API keys are scoped per user.
Code
guards.ts
// Guard middleware pipeline
async function runGuards(event: MCPEvent): Promise<GuardResult> {
const guards = [rateLimiter, injectionDetector, piiScanner];
for (const guard of guards) {
const result = await guard.check(event);
if (result.action === 'block') {
await logEvent({ ...event, status: 'blocked', guard: guard.name });
return result;
}
}
return { action: 'allow' };
}Results
- Reference implementation — not production-deployed
- Demonstrates sub-50ms guard evaluation on mock tool call payloads
- Live demo processes 100 events/minute within Upstash free tier limits
Screenshots
Source
Private implementation — code samples available on request. View on GitHub